Crypto Hacks in 2026: Record Losses and New Attack Tactics

Why Trust Web3Bet
Our team of experts has independently reviewed and evaluated all the products and services featured on this page to ensure you receive accurate and reliable information
The crypto market is increasingly being compared to the Crypto-Caribbean sea: the more “galleons” loaded with liquidity sail these routes, the more actively hunters circle them in search of loot. In this context, in addition to strong teams and successful products, those who search for a weak point, whether in code, infrastructure, or the human element, inevitably make their appearance.
In 2025, record-breaking levels of theft and a focus on damage from a few “mega-incidents” occurred, with North Korean groups associated with a significant force behind the threat. According to Chainalysis in its cybercrime report, more than 3.4 billion dollars were stolen from the crypto ecosystem in 2025, and the Bybit hack in February alone accounted for 1.5 billion dollars of that amount.
The case was also revealing: the exchange managed to quickly stabilize the situation and launch recovery efforts, while the industry, from exchanges and analysts to the on-chain community,y rapidly mobilized to track and block parts of the flows, becoming a rare example of the market’s collective defense.
What’s interesting in this article:
- Why the crypto market moved to a “few but deadly” model and how this changes risk management;
- The main hacker attack tactics that will shape 2026;
- What type of hacks will dominate in 2026;
- Practical advice on how to reduce the risk of hacking for projects and users.
“Mega-hacks” and what do North Korean hackers have to do with it?
How do hackers manage such hacks? Is the scale really that large? Let’s look at the diagram:
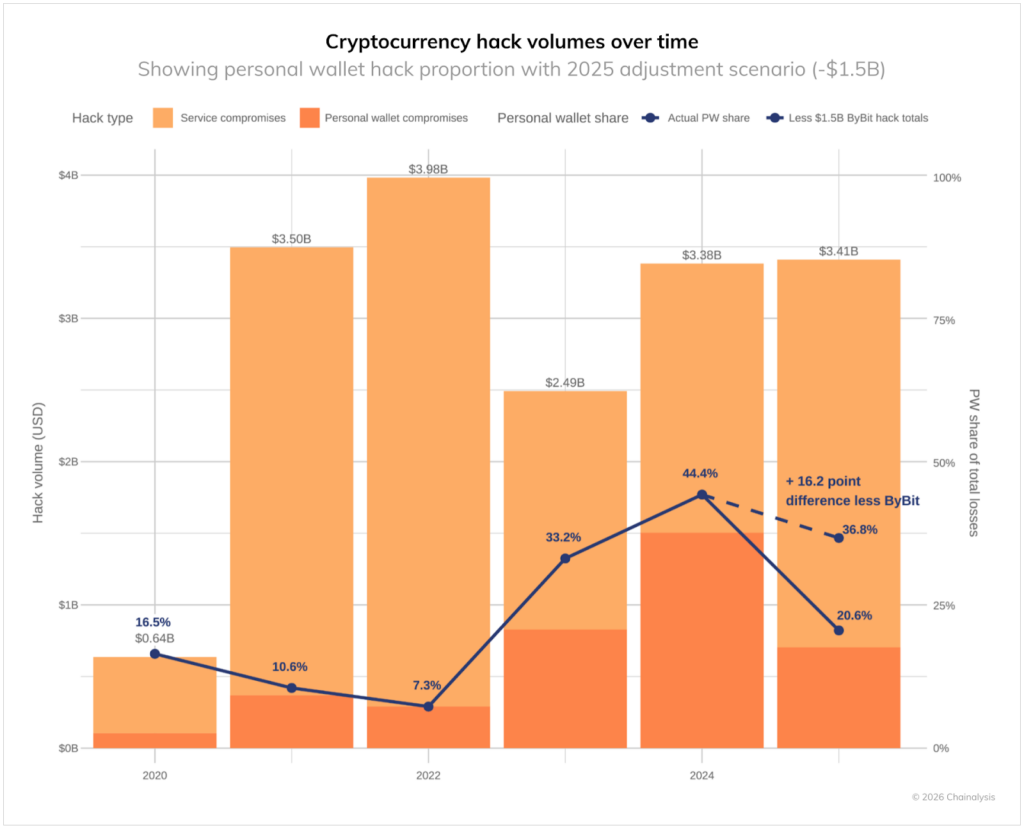
Cryptocurrency hack volume dynamics by year. The graph shows the growth of “user and service hacks.” Source: Chainalysis
Few but deadly: when “rarely” but worth billions of dollars
In 2025, hacks became more “large-scale.” The overall number of incidents might fluctuate, but the overall picture of the year is determined by a few catastrophic events. According to Chainalysis, the top three hacks represented 69% of all losses for services, and for the first time, the difference between the largest hack and the “median” incident surpassed 1000x. This means that the largest hacks have become comparatively much larger than “normal” incidents.
Why this matters: the risk model for the market is evolving. In a “few but deadly” scenario, what matters most is no longer “how often incidents happen,” but “whether a single incident can wipe out a meaningful share of reserves or client funds.” This is why the emphasis is on keys and access rights, limits and infrastructure segmentation, and emergency response plans, both on the platform and on the law enforcement side.
Tactic #1: Social engineering, compromising keys, and account accesses
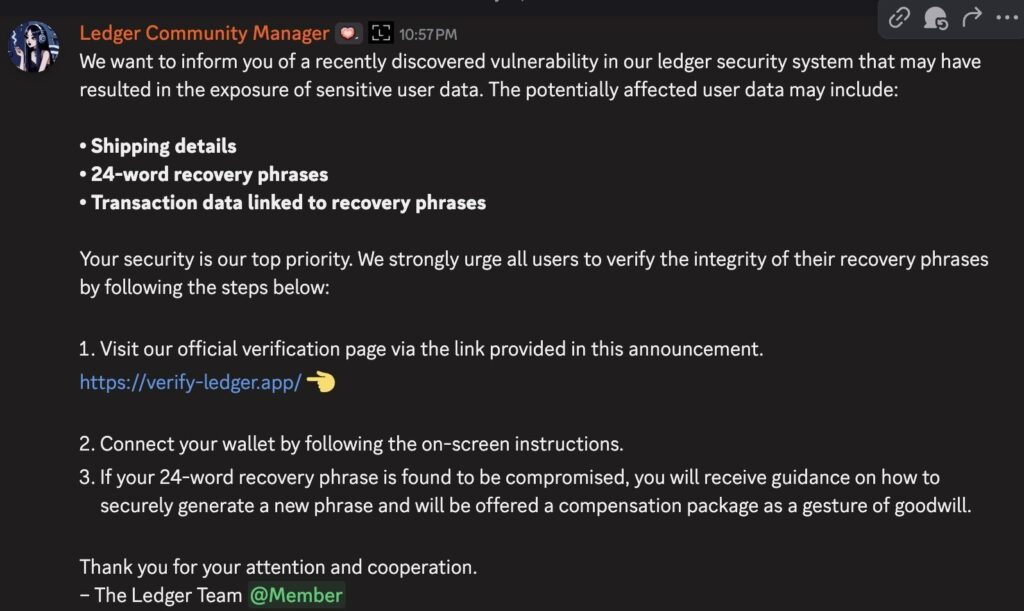
A phishing message in Ledger’s Discord: attackers, using a hacked moderator account, urged users to “verify” their seed phrase via a fake link.
If “few but deadly” characterizes the scale, then the first significant strategy for 2026 addresses the question of implementation mechanisms. An analytical report by Chainalysis emphasizes that centralized platforms suffer significant losses due to private key compromises. Although such incidents are less common than typical hacks of DeFi protocols, their consequences, in the form of large-scale thefts, account for the lion’s share of stolen funds.
It is significant that, according to Chainalysis estimates, private key compromises accounted for 88% of all losses among centralized services in the first quarter of 2025. This suggests that even with security services and significant resources, the fundamental elements, transaction signing keys, and the chains of access to them remain vulnerable.
The importance of this aspect in the context of North Korean groups is as follows. According to analysts, part of their “success” is increasingly driven not by finding vulnerabilities in code, but by gaining privileged access through internal company channels. One key method highlighted by experts is infiltrating IT specialists into cryptocurrency services or outsourcing critical work to companies to gain access to systems and pave the way for large-scale hacks.
At the same time, social engineering is also evolving. Instead of mass phishing campaigns, attackers prefer to operate indirectly, using private messages on instant messaging apps and social media. They pose as recruiters, partners, or investors, engaging victims in lengthy correspondence aimed not at clicking a link, but at gaining access to company resources. Potential victims may be induced to complete “test assignments,” run files for “interviews,” log into corporate systems, or share fragments of internal code and credentials. This approach is far more profitable than traditional *phishing.
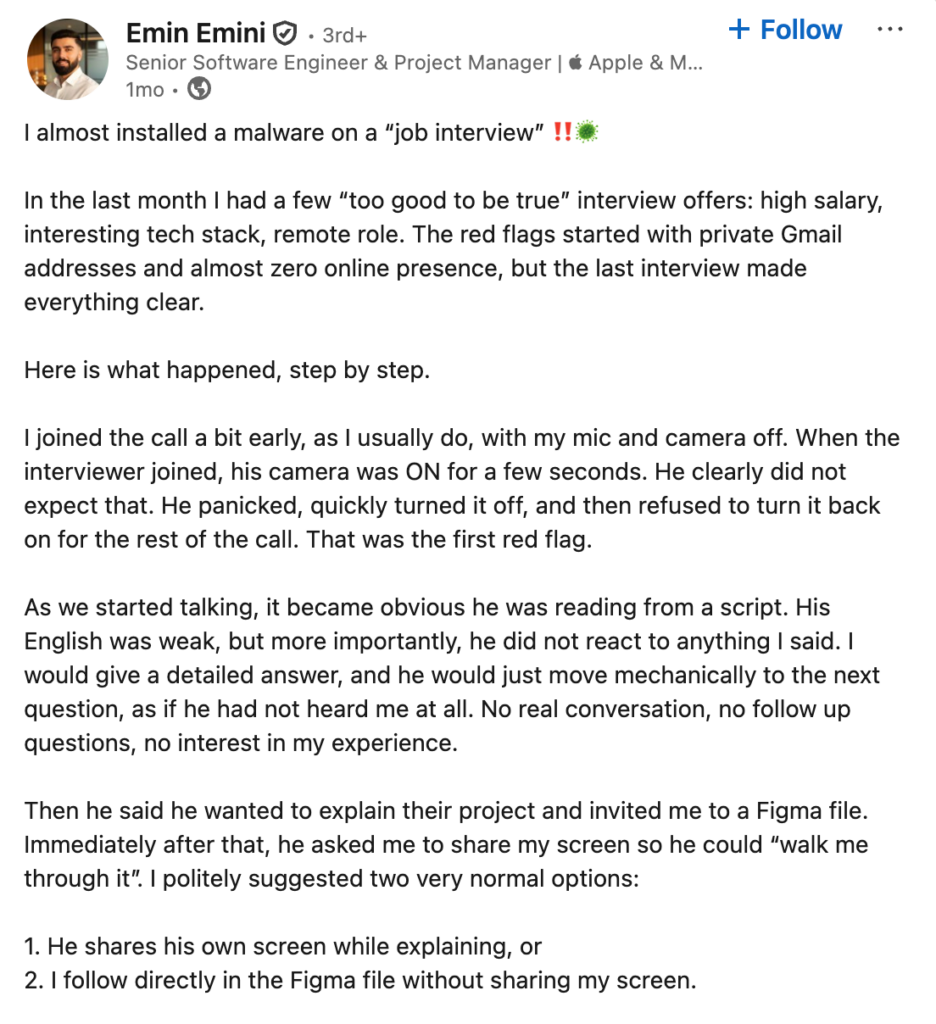
A LinkedIn post from a developer states that during a fake interview, someone attempted to infect his device and gain access through social engineering, using a lucrative offer: a high salary, remote work, etc.
There are also more extreme scenarios, which began to be discussed openly in 2025. In addition to recruitment and deception, the industry is discussing attempts at outright bribery of employees, especially in roles with low access thresholds but potentially useful for further advancement within the company.
For example, in public comments, the CEO of Coinbase mentioned that North Korean hackers attempted to bribe support staff by offering hundreds of thousands of dollars for internal access.
As a result, the risk shifts from a “bug in the code” to a “bug in the processes and people.”
*Phishing is an online fraud scheme in which attackers masquerade as an exchange, wallet, technical support, or a trusted person and, under various pretexts, trick users into granting access. Most often, the goal is to trick the victim into clicking a fake link, downloading a file, entering their login and password, 2FA codes, or seed phrase, and then stealing funds or taking over their account.
Tactic #2: Crypto-Drainers: Theft via “Permission,” Not Hacking
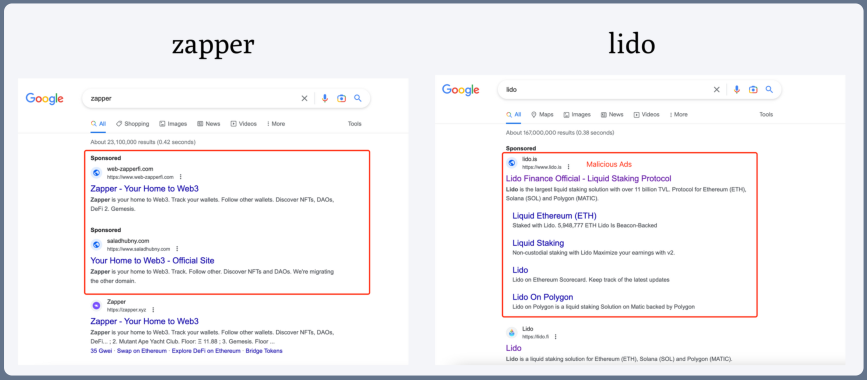
Google Ads with links to fraudulent cryptocurrency mining sites. Source: bleepingcomputer.com
In 2018-2025, when social engineering was actively employed to obtain corporate access, the crypto retail industry faced an increased threat: crypto wallet drainers. Rather than hacking, the attackers employed social engineering tactics, convincing users to sign transactions or make withdrawals. This leads to the depletion of cryptocurrency wallets as funds are transferred to the scammers’ accounts.
These attacks were often disguised as innocuous actions, such as “security check,” “account verification,” or “receiving compensation.” In reality, the user initiated the transaction through their wallet. The stolen assets can be withdrawn immediately or later if the fraudsters leave unrestricted access permissions to the funds. The scalability of drainers is ensured not by protocol vulnerabilities, but by the carelessness of a single user.
It is worth noting that crypto-drainers often operate in conjunction with phishing schemes, exploiting hacked administrator accounts, and creating fake job offers on popular messaging apps, such as Discord or Telegram, or professional networks such as LinkedIn, and recruitment agency websites. Incidents like the Ledger case, where a false “vulnerability” was exploited in a chat room, are not isolated incidents, but rather typical examples of how such fraudulent schemes are launched.
Tactic #3: Address Poisoning Schemes
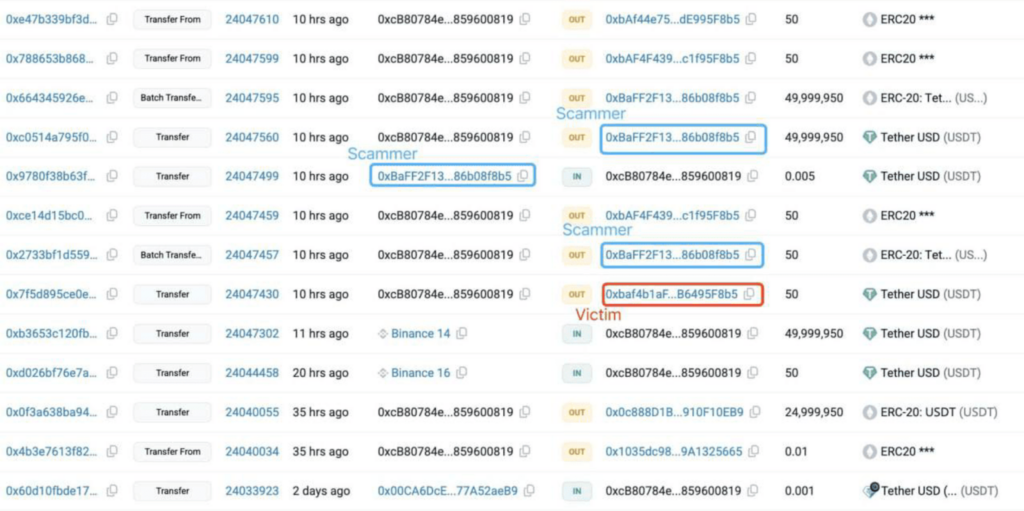
The screenshot shows an example of a scheme to poison addresses through transaction history: the fraudster created a transaction so that a similar address would appear in the history, and due to checking only the first/last characters, the user sent 49999950 USDT (≈ $50 million) not to themselves, but to the scammer.
Address poisoning (also known as Transaction History Poisoning) is a technique in which an attacker deliberately creates a transaction so that a “similar” address appears in the victim’s transaction history: visually resembling a familiar recipient address, an exchange deposit, or even one of the victim’s own addresses.
The effectiveness of this attack is not based on hacking skills, but on human negligence and behavior. This is because the user will copy information from the transaction history or a list of “recent recipients.” Consequently, the next time the user thinks they are sending money to a familiar address (“the same place they always send money to” or “to themselves”), they will actually be sending money to the attacker’s fake account.
The actual process of this fraud begins with the monetization process. Once the user sends a considerable amount of money to the wrong address, it is impossible to retrieve it. This is because the transaction has already been verified by the owner.
This type of fraud is expected to be more prominent in 2026. Its benefits include low development costs, high scalability, and high efficiency due to human error. This is because users with long addresses are more vulnerable since they only check the first and last characters of the address.
How to identify an attempt to poison an address
Let’s say you spot a suspicious transaction in your history. You’re absolutely certain you didn’t initiate it. Typically, it’s a transfer of an extremely small amount or some unusual NFT.
The attacker’s address turns out to be very similar to yours, and the beginning and end of the address are identical. This is an attempt to trick you into copying the erroneous address and transferring funds there.
2026 Attack Vector: Crypto Hackers Go After Retail
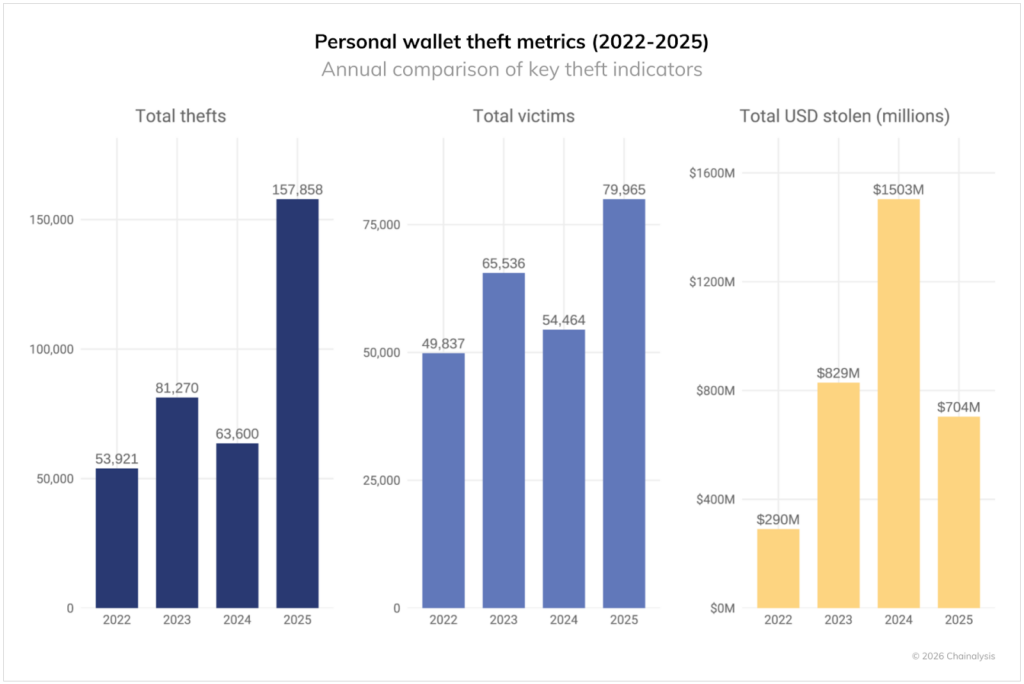
Web3 wallets fraud dynamics in 2022–2025: number of incidents, number of victims, and amount of stolen funds. Source: Chainalysis.
In 2025, there was a significant rise in the number of attacks on personal cryptocurrency wallets, with the number of incidents increasing to 158,000, and the total number of victims increasing to at least 80,000. A total of around $713 million was stolen from individuals. Although the total amount of damage was lower than the previous year, the number of attacks was substantially higher. This information does not include cases that victims did not report publicly.
According to Chainalysis experts, there is a change in the threat vector: while the defenses of centralized platforms are being strengthened, attackers are targeting more vulnerable areas – end users. Rather than attacks on large services, whose share has decreased, we see an increase in the number of private key compromises and attacks on individual wallets. This is referred to as “target shift.”
Some hacker groups, such as Lazarus, continue to focus on high-profile targets like exchanges and DeFi protocols, hoping to reap a hefty reward from a single successful operation. However, other criminals are shifting to mass attacks against retail users. Despite the lower average payout, these schemes generate a higher volume of victims and facilitate scalability through phishing, malicious extensions, address spoofing, and other common methods.
In 2026, further pressure on ordinary users is expected. Attacks against them are becoming more profitable for criminals due to fewer regulations, relaxed security practices, and the high likelihood of human error.
Savvy tips on how to protect yourself from hacks in 2026
Let’s take a closer look at how to best protect yourself from hacks. Below are tips to help you keep your digital assets safe:
1. Don’t store all your assets in one place
Similar to the Horcruxes from Harry Potter, separate your assets into roles so that one mistake doesn’t cost you your entire portfolio:
- “Cold” wallet: long-term, kept separate and not included in mints, drops, or tests;
- “Hot” wallet: everyday transfers and trading, minimum funds;
- “Trash” wallet: only for quests and various airdrop activities, should not contain valuable NFTs or large amounts.
*Horcruxes are magical objects or creatures in which a Dark wizard, such as Voldemort, has trapped a portion of his shattered soul in order to achieve immortality, making himself invulnerable for as long as the Horcrux exists.
2. Seed Phrase and Private Keys: Rules Without Compromise
- Never enter your seed phrase anywhere; it’s not needed for “checking,” “recovery,” or “verification.”
- Don’t send screenshots, photos, or the text of your seed phrase to anyone, even to “project supporters.”
- It’s best to store your seed phrase offline, preferably physically, without cloud storage or phone notes.
3. Two-factor authentication and access
- Not SMS, but an app or key;
- For exchanges and email, enable 2FA via the app, not SMS;
- It’s best to use a hardware security key for email and important accounts;
- Email is the master key: it’s used to reset passwords for exchanges, wallets, and social networks.
4. Protect yourself from “interview hacking”
- Don’t run test repositories or “test projects” on your main computer. Only through a sandbox.
- Don’t install “plugins” or “builds” from questionable sources.
- Maintain a separate virtual machine or computer for everything related to test tasks.
- If your interviewer asks you to share your screen, install “auxiliary software,” or open a strange link during the interview, this is a red flag.
*A sandbox is an isolated virtual environment that allows you to safely run suspicious programs or open untrusted files without the risk of infecting the main operating system or damaging important data.
5. Protection against wallet address poisoning
- Never copy the address from the transaction history if you’re transferring a large amount;
- Check not just the first and last characters, but at least 6-8 characters at the beginning and end;
- For large transfers, first send a test amount, such as $1 or $10.
6. *Crypto-drainers: signing transactions on autopilot
- Don’t sign transactions, especially if a website or project promises you an “airdrop,” “refund,” or “compensation” in an excessively large amount. In most cases, this is a scam.
- If your wallet shows “approval” for all tokens or “unlimited,” this is almost always a risk.
- Regularly revoke permissions from smart contracts and clear the list of granted permissions in your wallet settings.
Crypto-drainers are malicious software or scripts designed to automatically and completely drain all assets (cryptocurrencies and NFTs) from the victim’s wallet to the attacker’s wallet.
7. Most important: digital “hygiene of devices.”
Keep your operating system and browser up to date, and avoid pirated or cracked software. In most cases, they already contain malware.
Use a dedicated browser with a crypto profile, without unnecessary browser extensions.
Antivirus software isn’t a panacea, but it reduces the risk of simple Trojans and stealers.
Final tips to avoid consequences
If you feel that “something is wrong”, act as if there is a fire accident:
- Don’t try to fix the problem on the fly, and especially don’t continue working on the same device;
- From another known-clean device, immediately transfer the remaining assets to a new address;
- Then change your passwords and cancel all active sessions in your email and on exchanges.
Next, if possible, block withdrawals on the exchange, if such a feature is available, and contact support only through official channels. Any attempts to “sort out” the issue on a potentially infected computer often only worsen the situation and give the attacker time or access to launch a second attack.